- Bootloader Slot Count Not Found Moto G5s Plus
- Bootloader Slot Count Not Found Moto G5 G6
- Bootloader Slot Count Not Found Moto G5 Unlocked
- Bootloader Slot Count Not Found Moto G5 E6
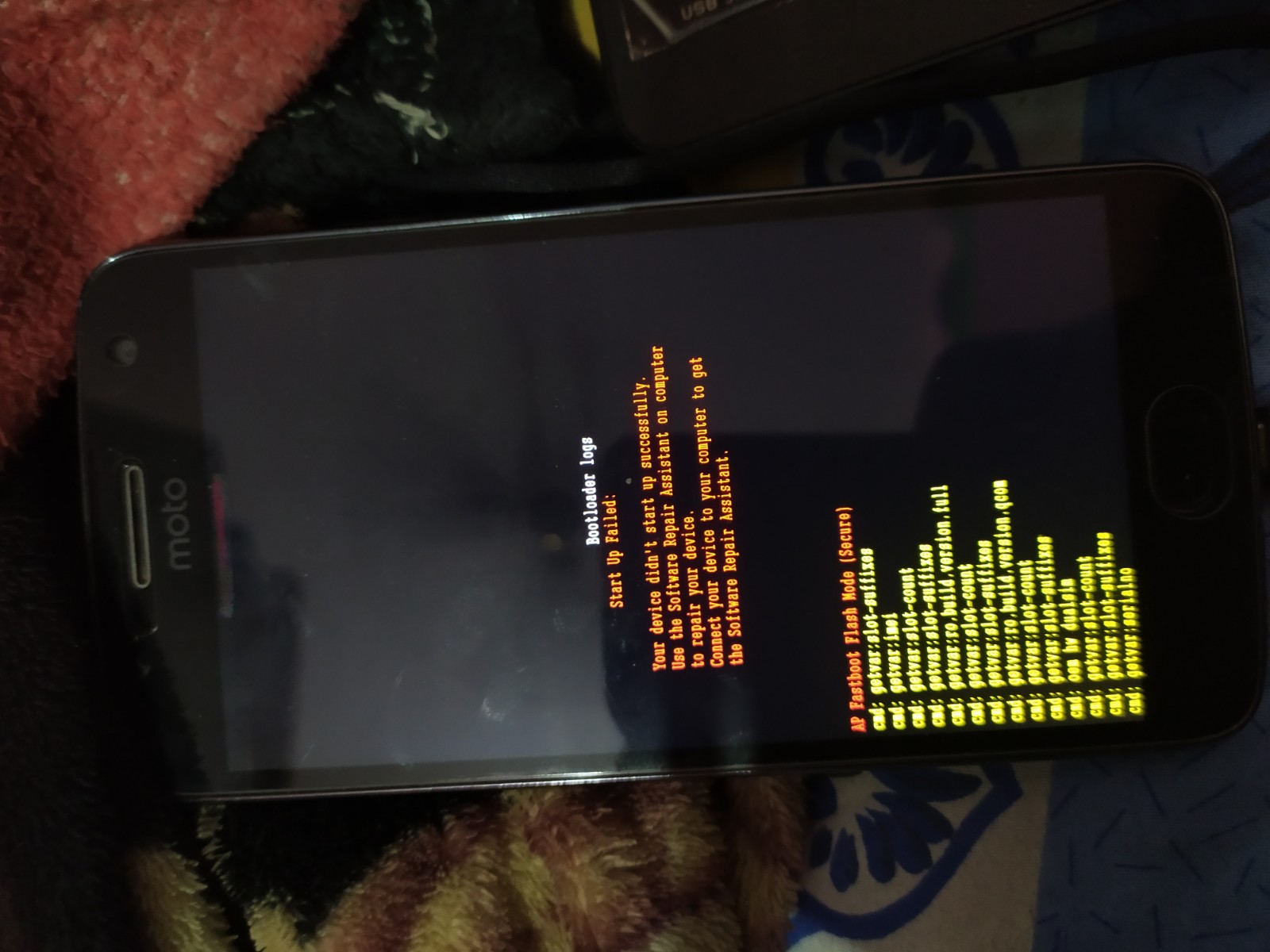
Moto G5 device in order to unbrick it. $ fastboot oem config cmdl foo = bar (bootloader) slot-count: not found (bootloader) slot-suffixes: not found. Boot Motorola Moto E5 Plus Bootloader Mode/Fastboot Mode using Hardware Buttons. Power off your phone. Once the device is off, press and hold the Volume Up + Power button together for a few seconds. Code: C: Program Files Minimal ADB and Fastbootfastboot getvar all (bootloader) slot-count: not found (bootloader) slot-suffixes: not found (bootlo MOTOROLA G4 XT1643 rebooting problem - GSM-Forum Welcome to the GSM-Forum forums.
In USENIX WOOT ‘17, that took place earlier this month in Vancouver, we presented our paper, “fastboot oem vuln: Android Bootloader Vulnerabilities in Vendor Customizations”, covering a year’s work in Android bootloaders research.
Our paper also includes some previously undisclosed details on CVE-2016-10277, a critical kernel command-line injection vulnerability in the Motorola Android Bootloader (ABOOT) that we had found and blogged about.
In the previous couple of blog posts, we demonstrated a tethered unrestricted root exploit against that vulnerability, that we later extended to other Moto devices - G4 & G5. Additional Moto devices have also been confirmed by the community.
In the WOOT’17 paper we describe a natural continuation of that exploit – a second stage untethered secure boot & device locking bypass (tested to be working on the vulnerable versions of Nexus 6, Moto G4 & G5). Moreover, we also present in the paper and this blog post other second stage exploits, such as persistent kernel code execution in Nexus 6, the ability to downgrade critical partitions (such as the bootloaders chain and TrustZone), unlocking a re-locked Nexus 6 bootloader, and more.
As usual, our PoC exploit is publicly available in our GitHub repo.
DISCLAIMER: Unlike the previous ephemeral jailbreak, the one presented today may brick your device. For example, during the development of it, we had to unlock our (luckily unlockable!) Moto G5 device in order to unbrick it.
Table of Contents
- Other Second-stage Exploits
– Persistent Kernel Code Execution on Nexus 6
– Unlocking a Re-locked Nexus 6 device from Platform OS
– Downgrade of Critical Partitions
– Modifying the system partition (Moto G4 and others)
Recap of the Vulnerability and the Tethered-jailbreak
- Vulnerable versions of the Motorola Android Bootloader (ABOOT) allow for kernel command-line injection.
- Using a proprietary fastboot OEM command, only available in the Motorola ABOOT, we can inject, through USB, a parameter named
initrdwhich allows us to force the Linux kernel to populateinitramfsintorootfsfrom a specified physical address. - We can abuse the ABOOT download functionality in order to place our own malicious
initramfsat a known physical address, namedSCRATCH_ADDR(see here for a list of devices). - Exploiting the vulnerability allows the adversary to gain unconfined root shell.
- Since the
initramfspayload is injected into RAM by the adversary, the vulnerability must be re-exploited on every reboot.
For example, here is a successful run of the exploit on cedric (Moto G5)
Persisting the Payload
Making an untethered exploit implies that we must somehow persist our payload. In general, although we have block-device write access with the unconfined root shell, due to Verified Boot we cannot make the system load with a tampered boot or system partitions.
It turns out, however, that our Moto devices have some unused partition we can populate our malicious initramfs into:
In addition, as was also suggested by Ethan Nelson-Moore, attackers can use the SD card partition (mmcblk1p1), if the device has one (shamu doesn’t, for example). Obviously, using the SD card does not require the first stage ephemeral exploit, as one can prepare it offline. It should be noted that a significant drawback of targeting SD cards, from the adversary perspective, is that it implies a physical attack only (unless the adversary targets a device with an already inserted SD card).
Owning the Unused Partition
The first step is to create an empty ext4 partition. At the host:
The next step is to populate the malicious initial ramdisk archive into the in-file ext4 filesystem. This can be done either on the host or on the device.On the device, one can replace the unused partition with the empty ext4 filesystem we have just created, mount it, and use cpio to populate the malicious initramfs. The attacker should also restore the SELinux contexts, and create the /sbin/init -> /init symbolic link – see the next section for more details.
The target partition now has the payload. It can be saved for later use on other devices (of the same model), i.e.
On other devices, populating it is now trivial:
Please note that the persisted payload may need some extra-massaging. For example, in order to overcome the tight size limitation of the cedric unused partition, we packed the binaries of the malicious initramfs (using UPX). In shamu, we had to a priori create some directories (/firmware, /persist), which are probably made by an init script. (This cannot happen on our readonly mounted root partition.)
Since we populated our malicious initramfs archive in some unused partition, we still need to lure Linux to use it as the root partition.
Forcing Linux to Use Our root Partition
Leaving many details behind, Linux prepares the root filesystem as follows (taking into account the Moto kernels config).
- It unpacks an internal initramfs to rootfs.
- It tries to populate a bootloader-supplied
initramfsfrom a physical address (initrd_{start,end}), specified in the Device-Tree Blob (DTB). In ARM/64 that can also be specified in the kernel command line by theinitrdargument. We abuse this functionality with the tetherd exploit. - If it fails, it reverts to an older
initrdmechanism, copying frominitrd_startinto/initrd.imageunderrootfs. - It tries to access
ramdisk_execute_commandwith a default value of/init(which can be overridden by specifyingrdiniton the kernel command line) on rootfs. If it succeeds, it will soon execute it and we are done. This is the normal flow on regular boots. - It will try to load
/initrd.imagefromrootfsinto/dev/ram0unless thenoinitrdargument is specified. It will then execute/linuxrcunless the ‘real’ root device is/dev/ram0. - If a
rootargument is specified, the kernel will mount it (read only, unless therwargument is specified) as the root filesystem. - If
execute_commandis specified (by theinitargument), the kernel will eventually execute it. If it succeeds, we are done. - The kernel will try to execute
/sbin/init,/etc/init,/bin/init,/bin/shin order until it succeeds, and panic otherwise.
We can thus conclude that the adversary can coerce Linux to use our tampered partition (e.g. /dev/block/bootdevice/by-name/padC) as the root partition by supplying the following arguments:
- Bogus
initrd, orrdinit=parameters in order to make the kernel fail on (2), (3) and (4). root=/dev/<real block name>to use our owned partition.rw. Optional. Only required for the factory initramfs archive if we do notrestorecon. (See above.)init=/init. Optional. Only required if we do not create the/sbin/initsymbolic link in the root partition. (See above.)
Hence, the minimum number of bytes which are needed to inject into the cmdline is 29-30 (depending on the partition). For example, on cedric, the fastboot command would be:
fastboot oem fsg-id 'a rdinit= root=/dev/mmcblk0p48'
Luckily (although we can also overcome this limitation, see next), ABOOT limits the string length of fsg-id parameter to 32 bytes before injecting it into the kernel command-line, so although we do not have much leeway with this UTAG, we managed to fit our payload in!
Putting it all Together: From shell user to untethered root
Kernel Command-line Injection from Platform OS
Before we created this very succinct payload (29-30 bytes), we had thought we wouldn’t be able find a payload that fit in the fsg-id UTAG. For instance, we incorrectly asserted that we would need to provide the rw and init arguments. We soon realized that by using initroot as a first stage exploit, we could cause ABOOT to inject another string into the kernel cmdline, which was much more spacious (256 bytes).
More importantly, what described next is independent of CVE-2016-10277 (in contrast to the previous payload), so if the adversary manages to gain a block-device access (with or without CVE-2016-10277), he can achieve a persistent root.
Kernel Command-line Overlay: cmdl
Interestingly, in our Moto devices (and also Nexus 6!) there is one UTAG which has caught our attention (in shamu this command will fail, although the UTAG is supported):
While very appealing, unfortunately this UTAG cannot be controlled from fastboot on production devices:
It’s a pity, because decompiling ABOOT!update_cmdline with IDA shows that this UTAG is limited to 256 bytes, more than enough of what we initially needed:
But can we use our block-device access (as we can achieve with the first stage initroot exploit) in order to control that UTAG?
Accessing the UTAGs Block Device
As explained above, using the unrestricted root we achieve with initroot, we can write on arbitrary block devices (which are not write-protected).The UTAGs reside under a device-specific partition:
Let’s examine one of them:
We can observe that our injected argument (fsg-id) is there. Basic understanding of the format can easily be achieved by just observing this sample:
- The UTAG name is specified alongside its type (e.g.
fsg-id:str) - At some offset from the start of UTAG, the number of data bytes are specified (
0x1cat offset0x4f) - The data is placed at a specific offset from the start of the UTAG.

Equipped with this knowledge, we can add our malicious cmdl UTAG.
Since this partition is NOT write-protected, we can overwrite it even if we are not running in recovery mode: (Kudos to @autoprime – at the beginning I thought one must use initroot in recovery mode for that, albeit it’s also possible by simply selecting recovery mode on the fastboot menu, during exploitation – that’s how we managed to overwrite the system partition on old Moto devices such as athene).
Bootloader Slot Count Not Found Moto G5s Plus
We can see that we indeed managed to inject our own data into the non-fastboot accessible UTAG!Again, being able to control this UTAG allows for a persistent root, independently of CVE-2016-10277 (given that you have block-device access).
Other Second-stage Exploits
In addition to the generic second stage exploit depicted above, we also describe in the paper and the following sections additional attacks. (Some are device-specific.)
Persistent Kernel Code Execution on Nexus 6
During our disclosure process, Android Security also observed that on shamu, an unrestricted root (as we gain with the ephemeral initroot), or one that runs under an SELinux domain with block device access, can overwrite the bootloader chain, boot, and system partitions. Due to incomplete Secure/Verified Boot implementation (verified on our re-locked Nexus 6 device), the boot partition is not verified, which implies a persistent kernel code execution – by using the ephemeral initroot exploit, the attacker can completely replace the boot partition with a tampered one (which makes the aforementioned second-stage exploit on Nexus 6 redundant), containing a malicious kernel image and an initramfs cpio archive. Afterwards, the attacker can simply reboot into fastboot, and remove the malicious utag. The attacker’s supplied kernel code and initramfs will then be loaded on every boot.
Bootloader Slot Count Not Found Moto G5 G6
Unlocking a Re-locked Nexus 6 device from Platform OS
Back in 2013, Dan Rosenberg found a vulnerability in the Motorola TrustZone kernel, allowing him to unlock the Motorola bootloader. In his blog, Dan depicted how Motorola implemented bootloader locking (also relevant for shamu), which can be summarized with the following state machine:
The transitions are as follows:
- The user first unlocks the device. The
WARRANTYVOIDqfuse is blown. This transition is governed by TEE thus it cannot be done from the Platform OS. - User re-locks the device. Bootloader writes an entry under the
sppartition, with an HMAC produced by TEE. - User unlocks the device. Bootloader removes that entry.
Conclusion: An unrestricted root (as one could gain by exploiting CVE-2016-10277) can unlock a re-locked bootloader by invalidating the sp partition.
We tagged this vulnerability as A-62345923.
Downgrade of Critical Partitions
As mentioned above, by being able to write on block devices, one can overwrite the bootloader chain (SBL1, ABOOT), TrustZone and other signed partitions (e.g. boot & recovery). Although such a replacement succeeds, due to Secure Boot, the boot flow will end in the PBL’s Emergency Download Mode (EDL) (verified on shamu) or fastboot, depending on which partition has failed verification. Despite that, since older images are perfectly-signed ones, downgrade attacks are possible, unless mitigated using the SW_ID field. It seems that Nexus 6 does not increase the SW_ID field between bootloader versions, thus the attacker can downgrade those signed partitions, allowing for exploitation of now-patched vulnerabilities in critical code. Other Moto devices are not immune too – verified on athene (that uses a different signing format), we were able to downgrade SBL1, ABOOT and TrustZone:
Modifying the system partition (Moto G4 and others)
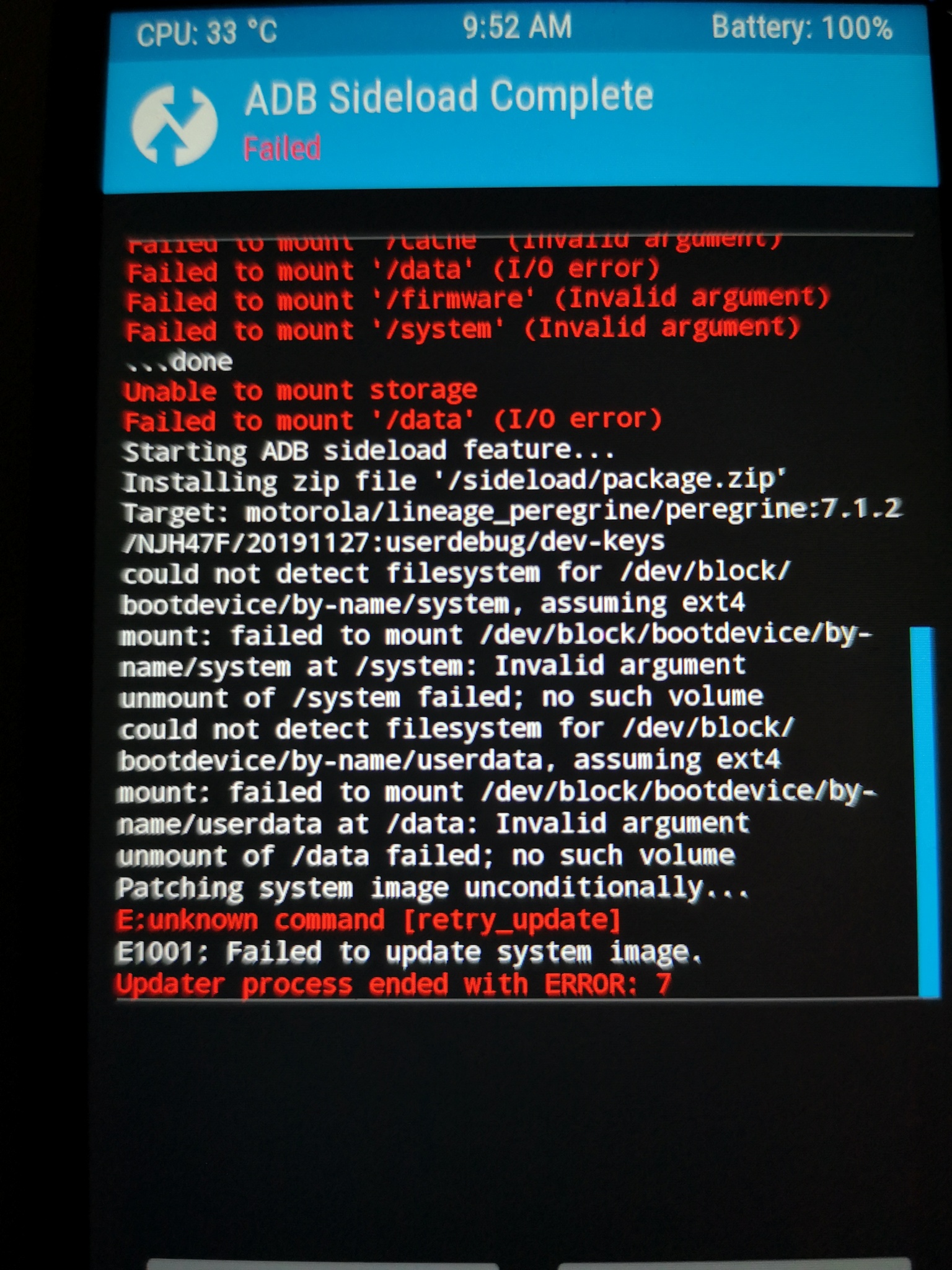
Due to secure boot, modifying the boot and recovery partitions on recent Motorola devices (such as athene & cedric) will cause the boot process to end in the fastboot mode. In order to achieve persistent code execution, the attacker, however, can aim at a different target – the system partition. Such a modification, however, is expected to be both prevented and detected by security controls. First, write-protection is enabled on the system partition (and others) by ABOOT upon boot. Unfortunately, this can be easily circumvented by the attacker by exploiting initroot slightly different – instead of instructing the bootloader to load the platform OS (by issuing fastboot continue), he can load the recovery OS, again, with the malicious initramfs injected into memory. Since the recovery OS needs write access on the system partition, the bootloader does not enable write-protection when booting into the recovery mode:
Then, the attacker can simply mount system and modify files. Sadly, although tampering with system can be detected by dm-verity, the fstab file under the Moto G4 boot image (and others), and in contrast to the G5 one, does not specify the verify attribute over the system partition. Controlling system allows the attacker to do much havoc. For example, the attacker now owns the Android runtime, can replace apps with malicious ones, can sideload privileged apps, and more.
Conclusion
In this blog we showed that having an ephemeral unrestricted root access is sufficient for achieving a persistent (untethered) jailbreak on affected Motorola devices. We demonstrated an end-to-end exploit for such devices, and also presented some other device-specific attacks.
The Moto G5 and Moto G5 Plus is a recently launched device from Motorola which comes with a locked bootloader. But with few simple steps, you can Unlock Bootloader of Moto G5 and Moto G5 Plus. If you decide to flash a ROM, root your phone, or to install a custom recovery, then you need to unlock the bootloader of Moto G5/Plus first. But you should be warned that unlocking Moto G5 bootloader may void its warranty. Follow the below guide to Unlock Bootloader of Moto G5 and Moto G5 Plus.
If you’re planning to install a custom ROM or want to root your phone, you have to unlock the bootloader of Moto G5 and Moto G5 Plus Force first. Once you unlock Moto G5 bootloader, you can root and install a custom recovery on your phone. So here is the step by step guide with the help of that you can Get Bootloader Key to quickly unlock bootloader of Moto G5 and Moto G5 Plus. Read the below note carefully before you unlock the bootloader of Moto G5/Plus.
Note:-
- Unlocking your device may void your phone warranty, and you won’t claim it back.
- Follow the steps correctly otherwise you may brick your device. We are not responsible for any damage to your phone.
- It will erase all your phone data, so we advise you first to take a complete backup of your phone and then proceed.
- Ensure that your phone has at least 50-60% charged to prevent the accidental shutdown in-between the process.
How to Unlock bootloader of Moto G5 and Moto G5 Plus –
1) First, enable ‘USB debugging’ and ‘OEM Unlock’ option from setting>developer option>. To enable Developer Options, go to About phone and tap the Build Number 7 times.
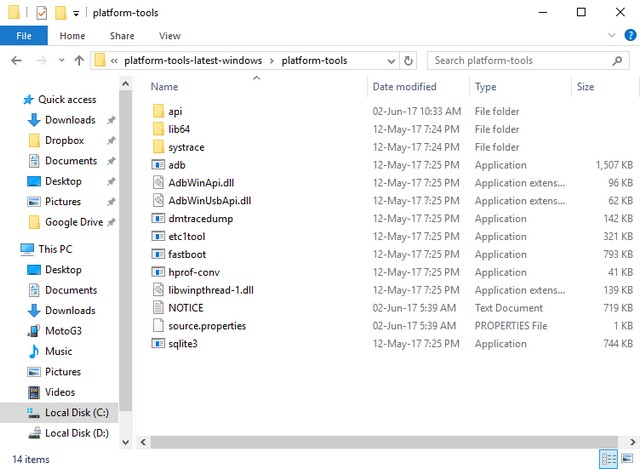
2) Install the ADB and fastboot driver for windows or ADB and Fastboot for Mac and then restart if you already have the driver installed then skip this step.
3) After installation of the driver, you can see a folder named ADB in your installation directory. Enter the folder, and you find four files including ADB and fastboot.exe.
4) Now press and hold ‘shift’ key and right-clicked anywhere in the folder and select ‘Open command window here’.
5) Now connect your device to PC and enter into the fastboot mode. To enter the fastboot mode of Moto G5 and Moto G5 Plus, type the below command in command prompt.
6) In the command window, type the following command.
Bootloader Slot Count Not Found Moto G5 Unlocked
7) the above command will return a string. Now copy the code in notepad and delete all the blank space so that you will get a single line string.
8) Now head over to the Motorola’s unlock the boot loader site and create a free account or Sign in Google+.
Bootloader Slot Count Not Found Moto G5 E6
9) Now Paste the above String (Unlock Code) in the bottom of the Moto site (step 6) and click on Can my device be unlocked? You also need to accept terms and condition on this page by clicking I Accept.
10) The unlock key will be sent to your E-Mail ID, which you used to register at Motorola site.
11) Now copy the Unlock Key and execute the following command.
12) The above command will Unlock Bootloader of Moto G5 and Moto G5 Plus.
13) Reboot and done.
This is the complete step by step guide on how to unlock bootloader of Moto G5/Plus. If you have any questions comment below.